Princeton, NJ - June 18, 2019 - Microsoft Windows RDP "BlueKeep" Vulnerability (CVE-2019-0708)
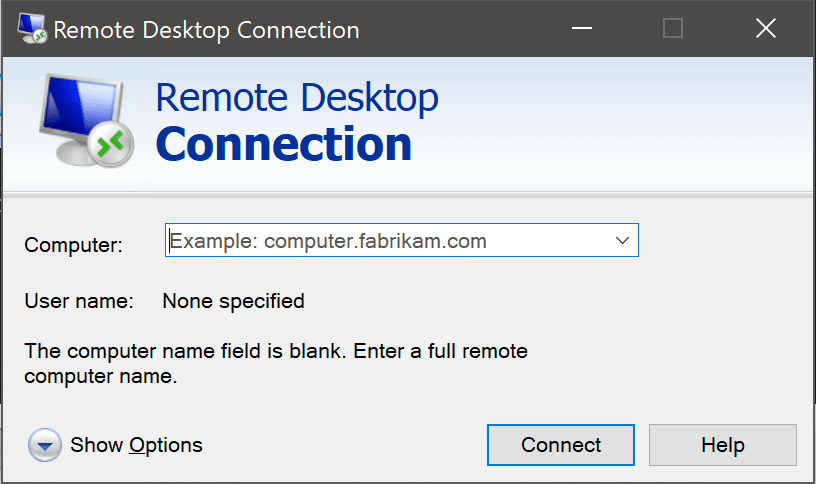
The CISA issued an alert to provide information on a vulnerability, known as “BlueKeep,” that exists in Microsoft Windows Operating Systems, both 32- and 64-bit versions. Blueclone has for the past several years advised clients to disable remote desktop services (RDP) on all servers unless controlled (accessible) via preset IP addresses within the edge firewall.
Blueclone clients on a Fully Managed Plan are not affected by this vulnerability as we've already proactively applied patches and disabled / restricted RDP access to only authorized IP addresses. Non Blueclone clients or clients that have opted to keep RDP enabled should consider the following mitigation strategies;
- Disable RDP on all servers and find an alternative connection method.
- Review the Microsoft Security Advisory and the Microsoft Customer Guidance for CVE-2019-0708 AND apply appropriate measures ASAP.
- Install all available patches.
- Upgrade end-of-life (EOL) Operating Systems. If your PCs are running an OS prior to Windows 10, now is the time to upgrade (Win 7 EOL is coming up).
- Disable unnecessary services not being used by the OS or installed applications.
- Enable NLA - Network Level Authentication.
- Block Transmission Control Protocol (TCP) port 3389 at the edge perimeter firewall and any ports that have edge rules that translate a different port externally to port 3389 internally (that trick no longer works). Since port 3389 is used to initiate an RDP session, blocking it prevents an attacker from exploiting BlueKeep from outside the user’s network.
- Finally if you don't have the resources to complete this internally, seek help and engage your IT Vendor asap to reduce exposure.
Blueclone Networks is a Princeton based IT Company with focus on Computer Systems Management, Cybersecurity, and Cloud Services for small & medium sized business in Central NJ.